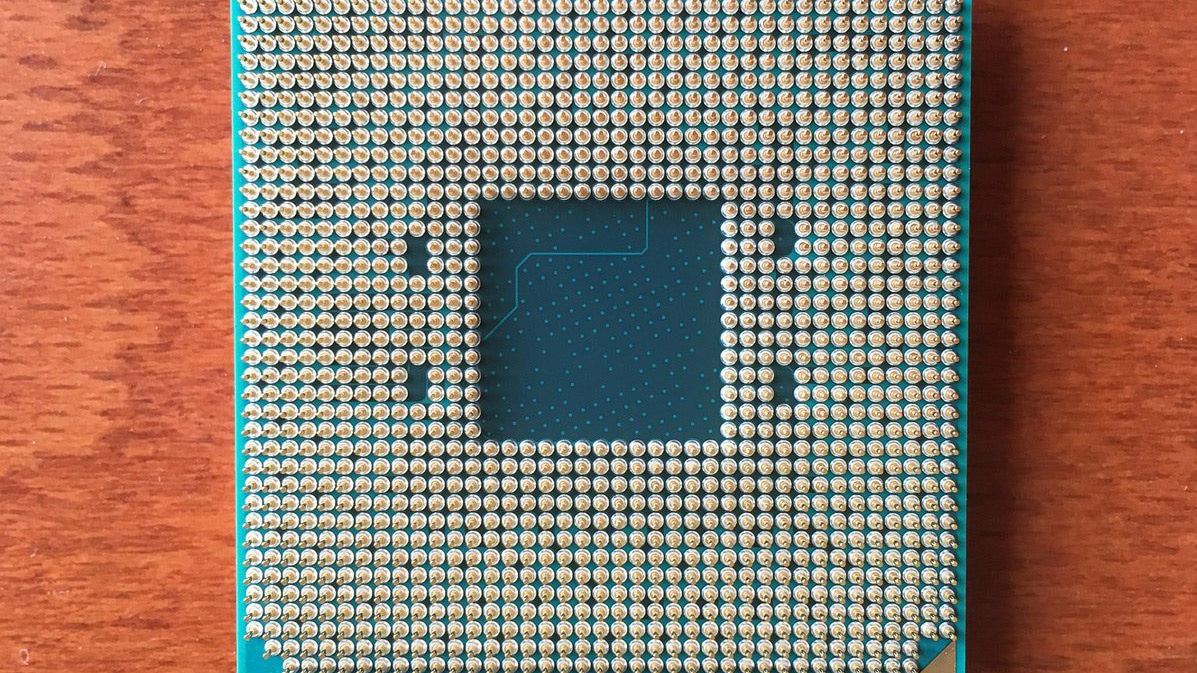
In the past few hours, a research paper published by a team from Graz University of Technology illustrated "Take A Way", a vulnerability behind which there are two side channel attack techniques that target AMD CPU from 2011 to 2019, including solutions based on Zen 2 architecture such as Ryzen 3000 or second generation EPYC. You can read more in this news.
In these minutes AMD has informed us that it has published one reply on the AMD Product Security page launched at the beginning of 2018 to inform users about the exposure of their architectures to Specter and Meltdown. Here is the translation of what is reported:
We are aware of a new document that reports potential security exploits in AMD CPUs, thanks to which an attacker could manipulate a cache-related functionality to potentially transmit user data in an unintended way.
The researchers then associate this data path with side channel vulnerabilities to speculative execution or known and already mitigated software. AMD believes that these are not new attacks based on speculative execution. AMD continues to recommend following best practices that help mitigate side channel issues:
- Keep your operating system updated using the latest versions and revisions of the platform's software and firmware, which include mitigation vulnerabilities based on speculative execution.
- Follow safe coding methodologies
- Implement the latest patched versions of critical libraries, including those susceptible to side channel attacks
- Apply safe computer usage practices and have an antivirus running
AMD therefore appears rather quiet the fact that the existing mitigations for other vulnerabilities constitute a more than adequate leverage against the problems raised by the researchers of the Graz University of Technology, to which the ball now passes. Obviously if there are further developments we will inform you promptly.