vpnMentor has discovered that customer data at YouHodler is not secure. For example, the research agency has discovered and linked thousands of recipient addresses and associated customer data.
More than 86 million records found
Data scientists Noam Rotem and Ran Locar, together with vpnMentor, discovered a large data breach at YouHodler, with more than 86 million records exposed. All this data is managed by YouHodler.
Before we continue about the leak, first something about YouHodler. With this platform you can lend your cryptocurrency. These are then immediately converted into US dollars or uhh European euros. In addition to Bitcoin, the lending platform supports BCH, ETH, LTC, XLM, XRP, DASH and a few other tokens. It is somewhat comparable to a pawnshop. You surrender something of value, you receive money, and you can buy it back later against commission.
Financial privacy is on the street
The research team discovered that the data breach allowed them to see a lot of privacy-sensitive information. Think of the full names, e-mail addresses, addresses, telephone numbers, birthdays, credit card numbers, CVV numbers, all bank details and recipient addresses.
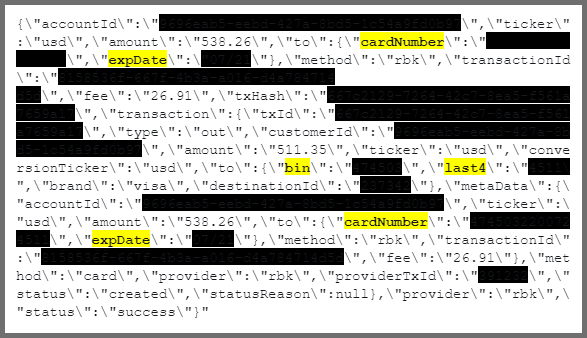
What the implications are, and how seriously YouHodler has failed here, is still being investigated. For example, the borrowing platform has labeled credit card CVV numbers (credit card verification) as “identity.” And these CVV numbers were not even fully coded. You can see that below:
In their own words:
In the example below we found the full card number and the expiration date, stored in plain text. The CCV number is not listed here. However, this shows that we have still found all the details needed to gain complete control over the map.
Link name and address data to wallet
In the same way the full names, addresses and bank details of the users such as account number and SWIFT code were displayed. In some cases, crypto recipient addresses were also displayed. vpnMentor:
It is very easy to link the above account to the bitcoin receiving address. Because of blockchain, the content of a wallet is always clear, even though they are intentionally anonymous. Linking a name and address to a wallet address can have serious consequences.
vpnMentor did not just run into this leak:
Ran and Noam are investigating ports to find known IP blocks. Once they have discovered IP blocks, they look for holes in the system that could indicate an open database. With the help of their technical expertise, they can confirm the identity of a leak in order to trace the data back to the owner. That is part of our web mapping project.
What could the impact be?
Malicious people could use this information to send targeted phishing emails, or directly hack into the user’s account. In addition, hackers can misuse the credit card details, as they have access to all necessary information. But it goes a little further:
It is always dangerous to have the full address of a user, and even more so if it can be linked to financial information. Thieves may have more reason to target users who have a lot of crypto. They can also use bank information for this.
There are also users whose recipient addresses were not visible, but who can also become targets. For example, targeted phishing emails.
In addition, most governments have their own resources to track users’ cryptic assets, but a data breach of this order can have even more dangerous consequences. Some governments, such as Egypt, have explicitly prohibited the possession of cryptocurrency. We have found customer information for users from Egypt.
After vpnMentor contacted YouHodler on July 22, 2019, YouHodler closed the leak the following day. All findings of the leak can be found in this comprehensive report.















