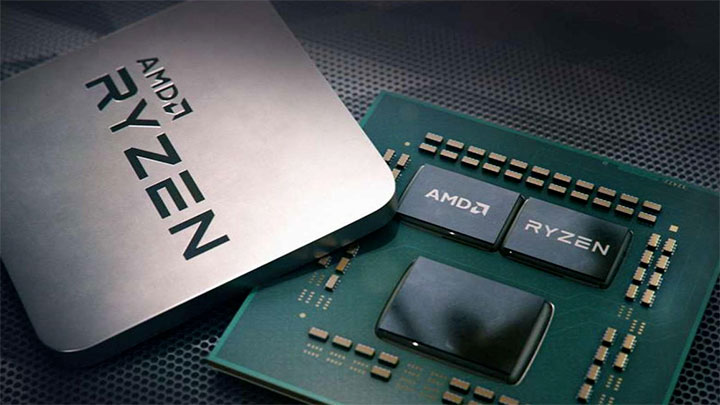
A research document released by Graz University of Technology illustrates the existence of a vulnerabilities in AMD CPUs that affects the solutions from 2011 to 2019, which also means i Ryzen based on Zen architecture, Zen + and Zen 2 are involved. Researchers have developed two new attack techniques generally renamed "Take A Way"and individually"Collide + Probe" is "Load + Reload", thanks to which it is possible to obtain sensitive data by manipulating the predictor of the L1D cache (L1 data).
The university claims to have communicated the existence of these issues to AMD on August 23, 2019, but there is currently no information on resolving these issues. Again, these are so-called "side channel attacks"to microprocessor architectures: from Specter and Meltdown at the beginning of 2018, research into possible flaws in computing architectures has become greater and the Intel CPUs have been most affected. AMD and ARM have almost come out unscathed, but this does not mean that are invincible.
"We did the reverse engineering of the way predictor from AMD's L1 cache in microarchitectures from 2011 to 2019, and this has led to two new attack techniques. With Collide + Probe, an attacker can monitor access to the cache victim without knowing physical addresses or shared memory during the sharing time of a logical core. With Load + Reload we exploit the way the way predictor to obtain traces of highly accurate accesses of the cache victim on the same physical core. Although Load + Reload relies on shared memory, this does not invalidate the cache line, allowing more stealthy attacks that do not induce any removal of data in the last level cache ".
The researchers claim to have exploited the vulnerability through a JavaScript that can run on the Chrome and Firefox browsers. The document indicates that through software and hardware solutions it is possible to fix the vulnerability, without however explaining if there could be possible performance repercussions.
Pending an AMD stance on the issue, you can read that in the document the research was funded by several sources, including Intel. "Additional funds have been provided through generous donations from Intel. Any opinions, findings and conclusions or advice expressed in this document are of their own authors and do not necessarily reflect the views of the lenders."
Although the name of Intel may open to easy conspiracy, it must be remembered that other studies financed by the company have discovered and communicated the existence of flaws on its architectures, therefore going against the financier himself. On the other hand, the house of Santa Clara has made no secret, even recently, of being actively involved in supporting the search for vulnerabilities on the part of people or external entities.
On Twitter the lead researcher explained that Intel supports some of its students and the university reveals all the sources from which it receives funding, adding that Intel does not limit the academic freedom and independence of universities and that the company has funded the program for two years. As for the vulnerability, the document reports that Intel has already patched a similar vulnerability in its processors.