New Malware Attack Stores Payloads in Windows Event Log
Security researchers have discovered new malware that uses the Windows event log to store malicious code. The researchers note that this is the first time the technique has been observed in the wild as part of a malware campaign.
The Trojan used in the attack is hidden in the system as it is not linked to a specific file on the system. Instead, the attacker places it in the Windows event log for future execution.
The threat actor has not been identified or linked to any of the active malware groups, according to Kaspersky.
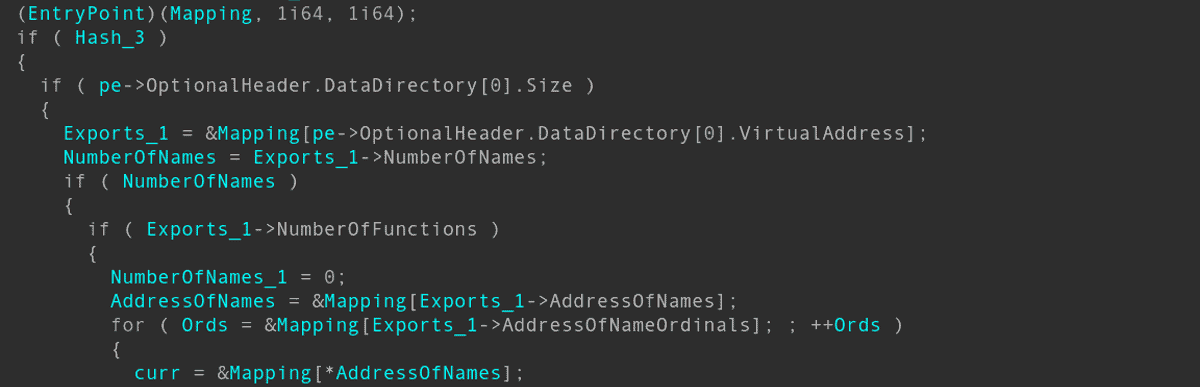
Kaspersky researchers describe how the malicious actor used various evasive methods and techniques to avoid detection on the targeted computer systems. The dropper modules were used in the attack to “patch native Windows API functions” that are related to event tracking and anti-malware scanning interfaces.
The sophisticated attack started in September 2021, when Kaspersky noticed the initial phase of the attack. The attackers used the Cobalt Strike framework in the attack, but the first step started at the user level. The target downloaded a RAR file from the file.io file hosting site and ran it afterwards. According to Kaspersky, different attack scenarios and techniques were used for other targets, but all attacks appear to have included initial reconnaissance of targets and preparations for further attacks.
The described method gave attackers the ability to inject code into processes, and this was used to inject additional modules into Windows and trusted applications. Cobalt Strike was not the only set of tools used by attackers. Kaspersky identified traces of the SilentBreak framework and several Trojans, ThrowbackDLL.dll and SlingshotDLL.dll, were named after the Throwback and Slingshot tools of the SilentBreak framework.
The file name of one of the droppers, sb.dll, could also be a reference to the framework, according to the researchers. Some of the tools appear to be custom built, and some feature names have been obfuscated to reduce the likelihood of detection and identification.
One of the analyzed attacks began with the injection of code into Windows processes after the initial infection had taken place. The dropper removed traces of earlier stages of the attack from the system as part of the detection evasion mechanisms implemented by the attackers.
It then copied the legitimate operating system error handler WerFault.exe to C:WindowsTasks and planted an encrypted binary resource called wer.dll in the same directory for DLL search order hijacking. DLL search order hijacking, often also known as DLL preloading, is a common form of attack that attempts to prioritize a malicious DLL file over a legitimate one.
Applications need to import functions from library files to use. The import is done implicitly or explicitly, and since Windows XP, a list of priority locations is used to determine the first candidate DLL. The first priority of the search order is the executable’s application folder; it is followed by the system directory, the 16-bit system directory, the Windows directory, and several other directories.
All an attacker needs to accomplish is to place the malicious DLL in a location that has a higher priority than the legitimate DLL.
It then added the newly created WerFault.exe to the OS autorun by adding it to SoftwareMicrosoftWindowsCurrentVersionRun for persistent access.
The wer.dll dropper is harmless on its own, as it requires the shellcode in the Windows event log for its execution.
Plant attack code in the Windows event log
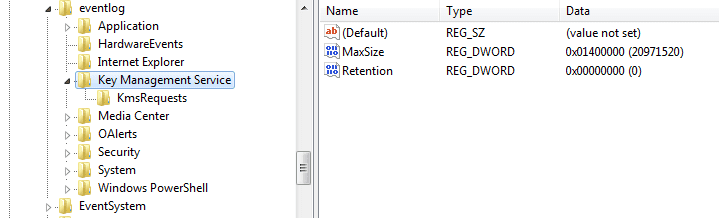
via Securelist / Kaspersky One of the unique aspects of the malware campaign was the use of the Windows event log for payload storage. The main advantage of this is that the fileless approach makes the payload harder to detect.
The dropper tries to upload the code to the Windows event log; if it does not exist, it is written as 8KB chunks using the ReportEvent() Windows API function. The data, if it exists, is loaded and then combined by a separate thread and then executed on the target system.
The launcher “passes control to the first byte of” shellcode according to Kaspersky research. It sends data that is used to execute the next stage of the attack:
- The address of the next Trojan used in the attack is revealed.
- A standard ROR13 hash of an exported function.
- Addresses of two strings, which become the “arguments of the exported function”.
Here again, evasion techniques were used to reduce the visibility of the attack.
The late-stage Trojan communicates with a C&C (command and control) server using HTTP with RC4 encryption or unencrypted communication with named pipes. Send an empty but encrypted string at the beginning to test the connection.
The late-stage Trojan fingerprints the target system, gathering information such as the computer name, local IP address, architecture, OS version, MachineGUID values found in SOFTWAREMicrosoftCryptography, and whether the process has SeDebugPrivilege.
The command and control server responds with its own code, which designates the next action the Trojan should take. Options include running custom commands, downloading files from a specific URL and saving them to a specific path on the system, getting a list of all processes and information, or injecting and executing shellcode into the process’s address space. destiny.
The named pipe-based Trojan is located in C:Windowsapds.dll, mimicking the legitimate Microsoft helper data services module library of the same name, which is located in C:WindowsSystem32.
Anti-detection techniques used by the attackers
The attackers used a wide range of anti-detection techniques to remain undetected:
- Using several different compilers-
- Whitelisted launchers.
- Use of digital certificates. 15 files were signed with “Fast Invest” certificates.
- Patch log exports from ntdll.dll.
- Shellcode placement in the Windows event log.
- C2 web domain imitation.
Kaspersky considers the use of the Windows event log for payload storage to be the “most innovative part” of the malware campaign. The entire campaign is sophisticated, using at least two commercial frameworks and various “types of late-stage RATs and anti-detection wrappers.”
Additional information about the attack is available on the safe list.
advertising