Pre-user account hijack attacks are on the rise
Most computer users know that criminals can gain access to their online accounts, for example, by stealing or guessing the password, through phishing or other forms of attack.
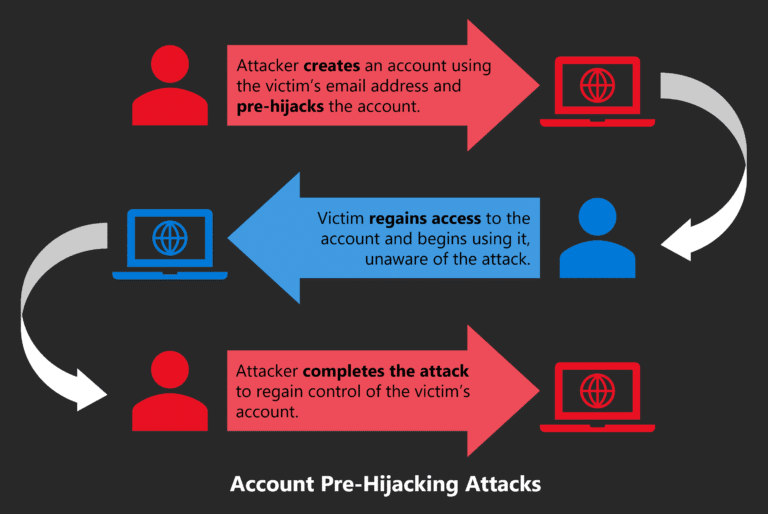
Many may not be aware of a new type of attack that is creating accounts with a user’s email address before the user does. Malicious actors use account hijacking attacks to prepare user accounts for full takeovers. The attacker creates accounts on sites and services using the victim’s email address. Various techniques are then used to “put the account into a pre-seized state.” Once a victim has regained access to the account, after discovering during registration that an account with the victim’s email address already exists, attacks are carried out to take over the account completely.
Not all websites and services are vulnerable to pre-account hijack attacks, but security researcher Avinash Sudhodanan believes a significant number are. Sudhodanan published the research article “Pre-hijacking accounts: An empirical study of security flaws in creating user accounts on the Web” in May 2022 in which he describes five types of pre-hijacking attacks.
Online account creation has evolved on the Internet. Previously, users used an ID and password to create accounts. Typically, these accounts were tied to a user’s email address. The method is still available on the Internet, but sites have also begun to support federated authentication, often in addition to supporting traditional account creation processes.
Federated authentication, for example Single Sign-On, adds a new layer of complexity to the user creation process, as sites and services often support both options. Companies like Facebook, Microsoft or Google support federated authentication and act as identity providers. Users Users can subscribe to third-party services that support single sign-on and user identity provider. Some sites allow users to link classic user accounts with single sign-on providers, unlocking the ability to sign in with a username and password, or the identity provider.
Websites and services have a strong incentive to support identity providers according to Sudhodanan as it “improves the experience for users”. Users can reuse accounts they have created in the past across multiple services; this makes the account creation process easier, faster, and can eliminate the need to set up account passwords. Previous research has shown that single sign-on providers become high-value targets for attacks.
Research focused on the security implications for existing accounts and less on the account creation process itself up to this point.
Pre-account hijack attacks
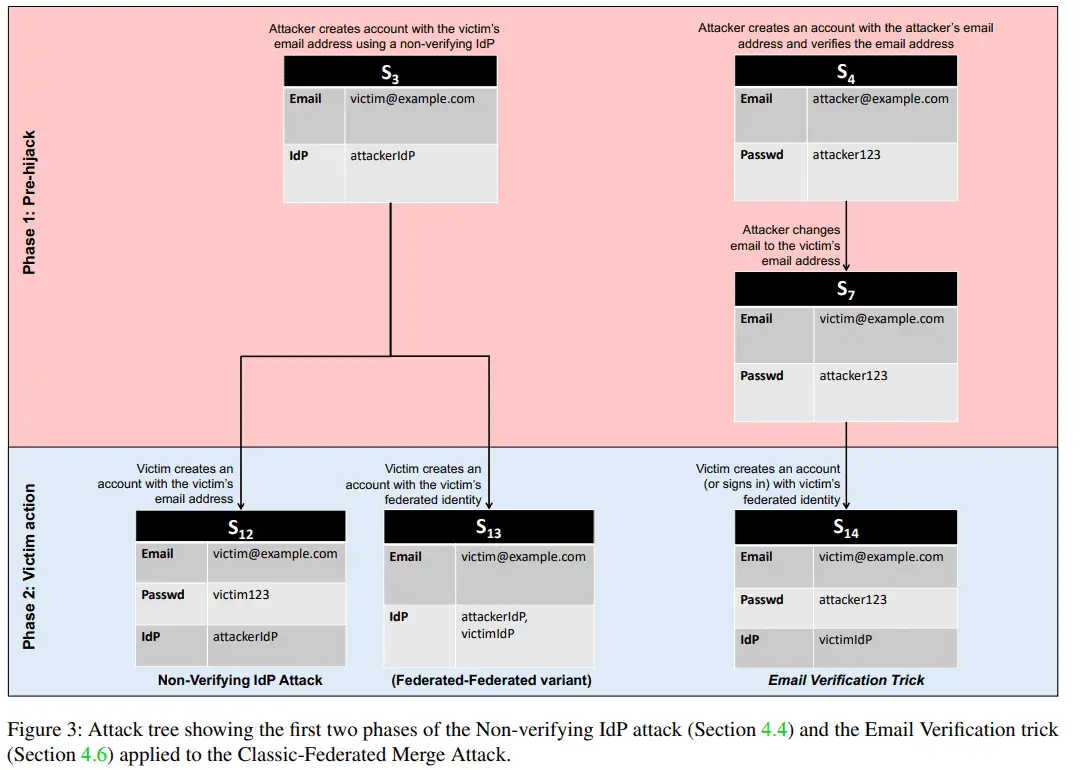
In his research, Sudhodanan shows that there is a whole class of pre-account hijack attacks. They all have in common that the attacker is performing actions on a target service before the victim. None of the five different types of attacks that Sudhodanan describes in the research paper require access to the victim’s identity provider account.
Attackers must target services that victims are likely to subscribe to in the future. Additional information, for example about existing accounts or interests, can help with targeting, but attackers can also target by popularity, trends, or even press releases if organizations are targeted.
The goal of pre-account hijack attacks is the same as that of classic account hijack attacks: to gain access to the victim’s account.
Depending on the nature of the target service, a successful attack could allow the attacker to read/modify sensitive information associated with the account (for example, messages, billing statements, usage history, etc.) or perform actions using the identity of the account. victim (for example, sending spoofed messages, making purchases using saved payment methods, etc.)
An attack consists of three phases:
- pre-hijack — The attacker uses the victims’ email addresses to create accounts on the target services. Knowledge of the email address is required to carry out the attack.
- victim action — The victim needs to create an account on the target or recover the account that already exists.
- account takeover attack — The attacker attempts to take over the user account on the target service using different forms of attack.
Classic Federated Combination Attack
The attack exploits interaction weaknesses between classic accounts and federated accounts at a single provider. The attacker can use the victim’s email address to create an account with the provider; the victim can create an account using the federated provider instead of using the same email address. Depending on how the service merges the two accounts, it could result in both parties having access to the same account.
For the attack to be successful, the target service is required to support classic and federated accounts. In addition, email addresses must be used as a unique account identifier and merging of both account types must be supported.
Once the victim creates the account using the federated provider, the target service can merge the accounts. Depending on how it is done, it may give the attacker access to the target service using the specified password.
Unexpired session attack
This attack takes advantage of the fact that some services do not log users out of their accounts if a password is reset. A victim can reset the password of an account on a service if the service informs the victim that an account already exists.
The attack works if the service supports multiple simultaneous sessions and if users do not log out of accounts if passwords are reset. The attacker must remain logged in to the account to keep the session active.
Trojan Identifier Attack
The attacker creates an account on the target service using the victim’s email address and any password. Once this is done, a second identifier is added to the account, for example, another email address that the attacker controls.
When the victim resets the passwords, the attacker can use the secondary identifier to regain access to the account.
Unexpired email change attack
The attack exploits a vulnerability in the email exchange process of target services. The attacker creates an account using the victim’s email address and any password at the beginning. The attacker then starts the process of changing the account’s email address; this leads to a confirmation email being sent to the new email address.
Instead of clicking the provided link right away, the attacker waits for the victim to reset the account password and retrieve it. The attacker will then activate the link to take control of the victim’s account.
The attack works only if the target service does not invalidate the links after a given period.
IdP attack without verification
The attack mirrors the combined classical-federated attack. The attacker creates an account on a target service using an identity provider that “does not verify ownership of an email address when creating a federated identity.”
The victim would have to create a classic account on the target service. If the service combines the two, the attacker can access the account.
closing words
Sudhodanan examined 75 sites out of the top 150 Alexa sites to find out if they are vulnerable to one or more of the described attacks. She found 252 potential vulnerabilities and 56 confirmed vulnerabilities during the scan. Dropbox, Instagram, LinkedIn, WordPress.com, and Zoom were found to be vulnerable to one of the described attacks.
The research work is accessible. here.
Now you: What do you do with account creation emails for accounts you didn’t start?
advertising